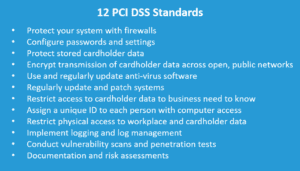
If you are a merchant who accepts credit cards and other digital payments, then you know that PCI compliance is a challenge. Keeping up with and understanding how the many rules and regulations affect your business is time-consuming and burdensome; however, when you consider how PCI compliance helps protect in the event of a breach, the effort is well worth it. As you may be aware, there are 12 mandated PCI compliance policies. We analyzed the 12 policies for you and put together the following suggestions to help with your compliance. But first, a quick review of the basics.
What is PCI DSS?
Payment Card Industry Data Security Standards (PCI DSS) are the globally accepted policies and procedures of the payment card industry. The Payment Card Industry Security Standards Council (PCI SSC), founded in 2006 by VISA, Mastercard, American Express, Discover, and JCB International, develop and maintain the PCI standards.
Organizations Which Should be PCI DSS compliant
All merchants, retailers and any organization who accept payment cards and process, store, or transmit cardholder financial information or authentication data must follow the PCI standards.
Use Only a Secure Network
The network you use to process payments must include a robust firewall intended to protect cardholder data. A firewall should exist between any wireless networks and the environment that holds cardholder sensitive data. Firewalls and secure networks are only as effective as the password(s) and security policies that your organization creates and regularly maintain. At a minimum, you should always change default passwords and never use default security parameters. A mandatory policy requiring the changing of passwords on a pre-determined schedule combined with multi-level authentication provides a strong defense against network intrusion.
Protect Cardholder Data
All organizations are required to protect cardholder data when cardholder data is stored on their network, and second, that the cardholder’s data is encrypted data during transmission. Encrypted data is impossible for thieves to use without the right encryption keys. The standards dictate that organizations not save card validation codes or PINs.
Manage System Vulnerabilities
Managing the vulnerabilities of your system is a must for any organization with cardholder data. At a minimum, use and update anti-virus software.
Systems and applications residing on the network must also contain security features that minimize intrusions and identify threats. It is a best practice to apply security patches, software, and operating system updates as they become available. With on-going ransomware, software injection, data skimming, and a myriad of other cyber threats, security features, systems, and software be monitored for vulnerabilities.
Sensitive cardholder data outsourced to third-party places the responsibility for maintaining a secure environment on the third-party provider.
Strong Access Control Features
PCI standards require access restrictions to the network and to defined file storage areas to protect sensitive data. Organizations should only release cardholder sensitive data to a third-party on a business’s need-to-know basis. Each person with access to network-connected computers should have unique log-in credentials, allowing the organization to monitor computer usage back to the individual and detect unauthorized access to network files or programs.
Organizations need to limit the number of individuals who can physically access cardholder data. Ideally, limiting those who have authorized access to sensitive data to a bare minimum is a best practice.
Fewer people with physical access make it easier to enforce security protocols, minimize exposure, and control unwanted intrusions.
Monitor, Track, and Test Networks
Every organization involved in accepting, processing, storing, and transmitting payments must track users and their access, run threat assessments, and test against potential access threats to company and cardholder from outside the organization. Completing a self-assessment questionnaire (SAQ) and an annual Attestation of Compliance is required to be PCI DSS compliant. There are three versions of the Attestation of Compliance, just as there are five versions of the Self-Assessment Questionnaire, Requirements for each SAQ are here https://www.pcisecuritystandards.org/documents/Understanding_SAQs_PCI_DSS_v3.pdf
An example of a Self-Assessment Questionnaire and attestation for card-not-present merchants with all card data functions fully outsourced can be found here https://www.pcisecuritystandards.org/documents/SAQ_A_v3.pdf
Adopt and Maintain Information Security Administrative Policies
Every organization involved in a payment card transaction needs to have information security policies for each position for safeguarding data, specifically cardholder data. Policies should cover day-to-day operations as well as the steps required by each position in the event of a breach. Policies should detail the type and frequency of information security policy training.
Summary
PCI DSS compliance is a necessity for every organization involved in the payments industry. As noted previously, merchants can move a significant amount of time and expense of compliance to third-party providers like IntelliPay. IntelliPay’s intelligent payment platform and payment gateway limit public network exposure and ensure compliance with PCI DSS, continually changing state laws, and card network rules and regulations. For more information or to experience the benefits, IntelliPay can bring to your organization, contact sales at 855-877-6632 option 3 or via email at sales@intellipay.com.

